Networking Devices
Hubs, Switches, Routers, Modems, and Firewalls
Knowing what hubs, switches, routers, and modems do can be helpful if you notice any issues while browsing the Internet, especially if you want to stream movies or play games online. Understanding basic networking hardware can help you connect devices, share information, and keep your data secure. We introduce the components you are most likely to encounter at home, in a campus lab, or in an office setting.
Hub vs. Switch
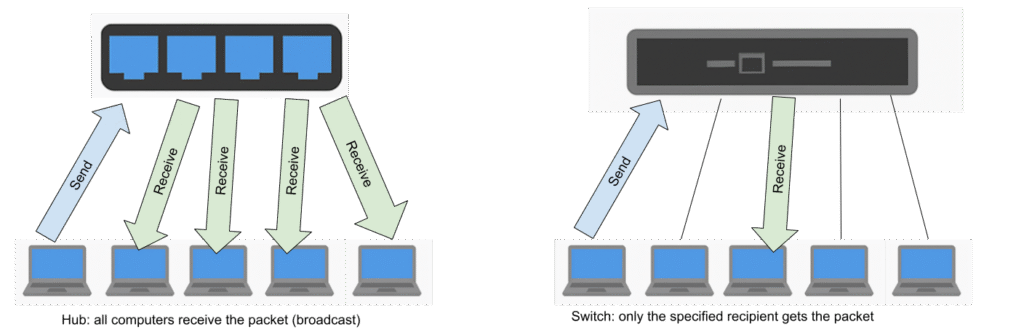
Hubs broadcast data to all connected devices. This is inefficient and insecure (every device sees every packet). They’re rarely used today. Ethernet started as a broadcast-only network. Each node on the network could see messages sent by all other nodes, either by being on a common wire or a network hub, a simple repeater that took every packet it received and rebroadcast it to all the outputs.
Switches are smarter than hubs: switches direct data only to the intended recipient device, reducing unnecessary data exposure. Modern Ethernet uses switches rather than hubs1 due to their efficiency and security benefits.
Router
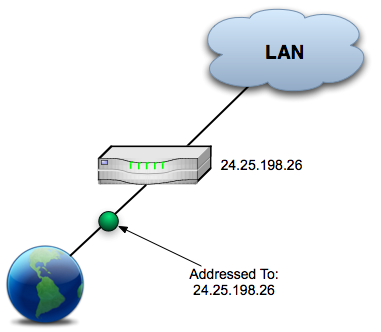
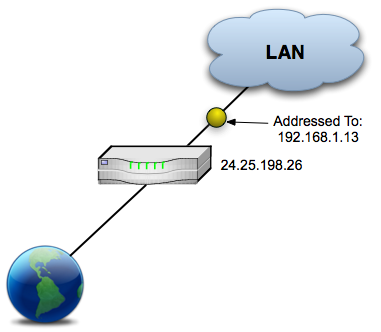
A router connects one network to another, like your home network to the Internet. It decides the best path for data to travel between networks. A routing configuration table keeps track of all connections to the router and all possible paths that exist between networks. The router uses the configuration table to choose the quickest/best path for data.

Most home routers include a built-in switch and wireless access point, and often have firewall features too.
Modems
A modem (MOdulator-DEModulator)2 translates digital signals from your network into analog signals that travel over telephone or cable lines. It also translates analog signals back to digital. Your Internet Service Provider (ISP) provides one for Internet access.
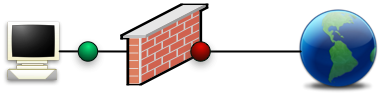
Firewall
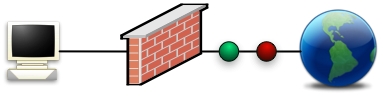
A firewall uses rules to filter network traffic. It blocks unauthorized connections and allows trusted ones from entering or exiting the network. Firewalls can be physical devices (hardware built into routers) or software running on a computer.
How does networking affect me?
Streaming means that your computer is constantly sending and receiving tiny pieces of data known as packets. Packet loss happens when some of those packets get delayed, dropped, or corrupted somewhere along the path.
This can be caused by:
- Weak Wi-Fi signals or interference (e.g., walls, microwaves, other networks)
- Congested networks, especially during peak hours
- Old or overloaded routers or switches
- Poor routing paths between your ISP and the game server
- ISP issues or throttling
In a video game, if you are experiencing packet loss:
- Your actions might appear delayed (lag)
- Characters might teleport (rubber-banding)
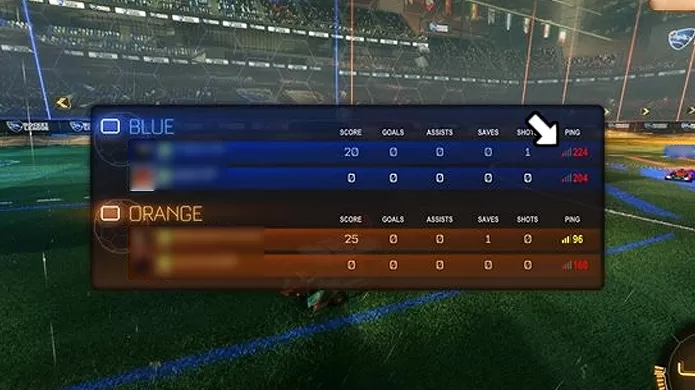
In the below screenshot, the ping is evident for each of these players in Rocket League. Note the red ones are numbers like 224, but the yellow one is 96. If you have better internet, you might see a green 24 or even a lower number!
Hints to help you with packet loss: use a wired connection (Ethernet) when possible, restart your router, or test your connection with tools like ping or traceroute to see where packet loss might be happening.
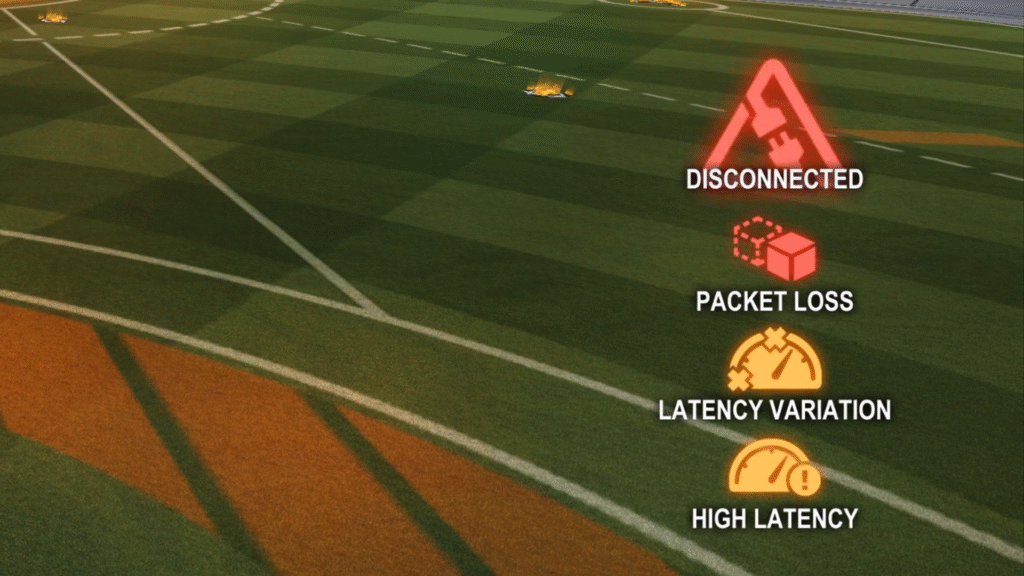
There are all sorts of connections issues you might have in Rocket League (and other games):
Exercises
- Your home router likely has a firewall with basic security rules.
- Access your router settings (via IP address) and identify firewall settings. Document what you find.
- Other than computer networks, where have you heard terms like hub or switch, and do they work analogously? For example, a bicycle has a hub and spokes, and airlines have a hub. Railways have switches. Any other examples you can think of, or can you expand on the ones given here?
- Explore: are hubs used anywhere anymore in networking, or are they totally obsolete nowadays?
- We didn’t talk about it much, but TCP and UDP are different protocols for sending data. UDP is better for streaming video compared to TCP based on things like how it handles packet loss. What might you prefer to use TCP for, then?
- Do you play any games online, such as Rocket League or Minecraft, and if so, what connection issues have you had with them? Do you stream movies online?
- Reference: CS 161 ↩︎
- Reference: CS402 Saylor ↩︎
