Threats
Malware
Malware is a portmanteau of “malicious software”123. We’ll go through some examples of types of malware. Note that there is overlap between types of malware — ransomware could be a trojan or a virus!
Malware can target any type of computer system, e.g.,
- PCs and servers
- mobile devices
- process control systems
Malware that Spreads
- Virus — Malicious code that is spread through infected programs or files (e.g., Excel macros or PDF files)
- Worm — Directly uses a network service to spread itself. Typically exploits a vulnerability in a target to execute code that then exploits more systems
- Trojan Horse — malicious software embedded in what appears to be a useful program
Typically, worms are self-propagating and spread without user interaction, whereas viruses require users to do things like copy an infected file.
Malware that Hides
- Rootkit: A secret program designed to give back door privileged access to a system. Obtains “root” privileges, and often embeds itself in kernel code
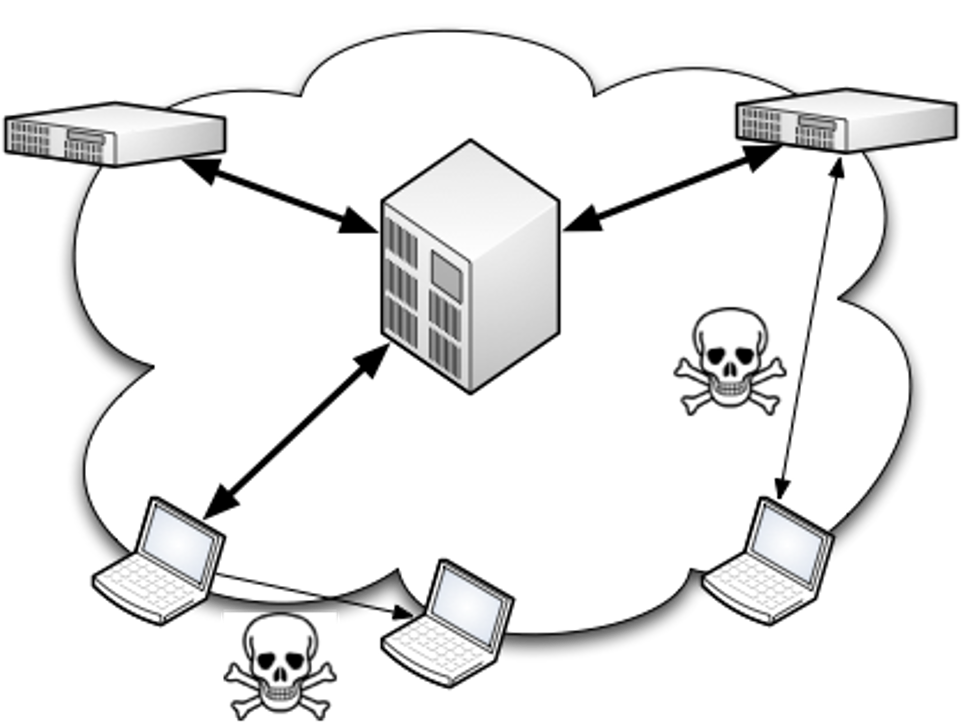
- Bots and Botnets: A bot is a host, or computer, that is infected with malware that accepts remote commands from an attacker. A botnet is a network of exploited hosts controlled by a single party.
- Backdoor is a way to access a device bypassing normal entry points and access control. It allows ongoing stealthy remote access to a machine, often by enabling a network service. A backdoor program contacted via a backdoor may be used for malware installation and updates. These may come from program flaws or be intentionally built in by the developer.
Ransomware/Spyware
- Ransomware is malware designed to extort the user in exchange for access to something of value. Often in the form of “Pay or I’ll post your private data to the Internet.” Sometimes also referred to as “Scareware”. A common form is a fake anti-virus program that claims you have many viruses and must pay for the full version to get rid of them.
- Spyware is focused specifically on gathering information about you. Think: data mining.
- Adware is software that generates revenue by automatically displaying online advertisements in the user interface or on a screen presented during the installation process. In some cases, it can track online behavior to display personalized ads.

Spyware allows an attacker to gain remote access to a target’s data without the user knowing. Data includes messenger logs, photos, files, and contacts. Attackers can also do real-time surveillance, for example, by accessing the device’s microphone and cameras.
Attacks can relay the data to advertisers or other interested parties. Spyware can infect a computer as a software virus or as the result of installing a new program. If a user knows they’ve installed a data collecting program and understands what data is being collected and with whom it is being shared, then it is not strictly considered spyware.
Spyware and adware can cause many recognizable problems on infected computers, such as slow computer function, jumpy internet, and altered home pages in the web browser. While spyware and adware can affect any OS, Windows users are the hardest hit. This is due to the fact that Windows is the most widely used OS across the world.
You may have seen internet ads claiming that your computer is infected with spyware or viruses and asking you to click for a “free scan.” Unwary users may click on these ads, leading to a download that will infect the user’s computer with malware, all while telling the user that it is removing threats from the computer. You should avoid clicking on such ads.
Keyloggers
- Software that records and send user keystrokes to an attacker, or
- Hardware of some small, inexpensive memory device plugged in between a keyboard cable and a computer
Could be used to get your password!
Drive-By Downloads
Simply visiting a web page can result in malware being silently downloaded and run on the user’s device without the user knowing about it!
Zero-Day Exploits
A zero-day exploit (zero-day) takes advantage of a software vulnerability that is unknown to the developers. The day a vulnerability becomes known is the first day, and the attack precedes that — that’s why it’s called zero-day!
Examples
Adobe Flash had many Zero-Day Exploits. Adobe finally End-of-Life’d Flash in 2020!
- February 2 2015 – Adobe Flash – CVE-2015-0313
- March 12 2015 – AdobeFlash- CVE-2015-0332 – CVE2015-0342
- April 14 2015 – AdobeFlash – CVE-2015-0346 – CVE- 2015-0360 + more
- 26 October 2016 – Adobe Flash – CVE-2016-7855
- 11 April 2017 – Adobe Flash – CVE-2017-3058 CVE-2017-3064
If interested, you may read this book to learn more about cyberwarfare, and zero-day exploits in particular!
(The link takes you to the library website)
How You Can Get Infected
- E-mail attachments
- Example: files with malicious scripts embedded: Microsoft Warns of Tax-Themed Email Attacks Using PDFs and QR Codes to Deliver Malware
- Example: via social engineering
- Instant messaging links and attachments (such as on Discord or Telegram)
- Pirated Software (Trojans are often embedded in illegal ‘warez’)
- Infected USB drives or other removable media
- File downloads (many backdoor Trojans are embedded with other files)
- Unreliable download sources
- Browser extensions
- File-sharing applications
- Program installers that can be downloaded from the internet may “bundle” other software into the installation.
- Fake mobile apps from third-party app stores
- Clickfix, where the visitor to a hacked or malicious website is asked to distinguish themselves from bots by pressing a combination of keyboard keys that causes Microsoft Windows to download password-stealing malware.
Avoid running programs you don’t need to prevent unwanted access to your computer. When installing new software, you must read each prompt the installer puts on the screen to make sure that software is not being installed inadvertently.
How to protect yourself from viruses
- Enable antivirus software and keep it updated (any anti-virus from the approved list, including Defender).
- Keep your operating system and software up to date
- Don’t open unexpected file attachments, even from friends. If in doubt, ask the sender.
- Avoid running programs or downloads from unknown sources.
- Avoid opening unrecognized attachments, especially those that do not come through a mail provider that screens for malware
- NCSU’s Gmail screens attachments for malware, though this is not a guarantee.
- If you know the person who sent you a file, but were not expecting it, you may want to contact them before opening it. Many viruses automatically send themselves out to addresses found in files on an infected computer.
- Before running a download from an unknown site, or opening an e-mail attachment, always scan it to ensure that it is not infected. If you do not know the source of a file, do not open it.
Phishing
Phishing relies on impersonating a trustworthy entity to steal information or credentials from users. The type of information stolen from phishing messages can be any type of personal/sensitive data — for example, social security numbers, credit card numbers, phone numbers, or login credentials. Phishing can take many forms, such as emails, messages, and even QR codes. Phishing overlaps with similar concepts like scams or fraud.
Specific Examples
- Example 1: You get an email from a professor’s unityID@yahoo.com, asking you to immediately run to the store to purchase gift cards, as they forgot to buy presents for their kids. They will not forget this and will reimburse you.
- Example 2: You get a text message stating that your bitcoin balance on totallyBitCoinWallet.notascam.com is 900 bitcoin. To sign in, use the password hunter2 and username lucky.
- Example 3: An email from a university address that just states, “call me 555-122-2222”
- Example 4: You scan a QR code on a parking meter; the website looks identical to what you are used to; however, the domain reads totallyParkingMeter.notascam.com.
- Example 5: You get a call from NCSU University; they tell you that you need to immediately change your password and that they can do it over the phone.
- Example 6: You are sent an invoice on your email, body just says “see attachment below” and the attachment is what appears to be a invoice.pdf.
- Example 7: An email claiming that NCSU needs to audit your financial records, or you will be forced to pay back your financial aid, you can either respond with your UnityID/Password or upload a PDF of a list of documents at the link provided.
Examples 1 and 3 are widespread scams that target academics, and example 2 is pulled from prior work that studied SMS phishing attacks. In all of the examples above, there is a sense of urgency, which is what these actors rely on to steal your information or gain access to your machine.
Example 6 is a tricky one, on one hand, it could be a legitimate invoice, however, malicious PDFs never go out of style.
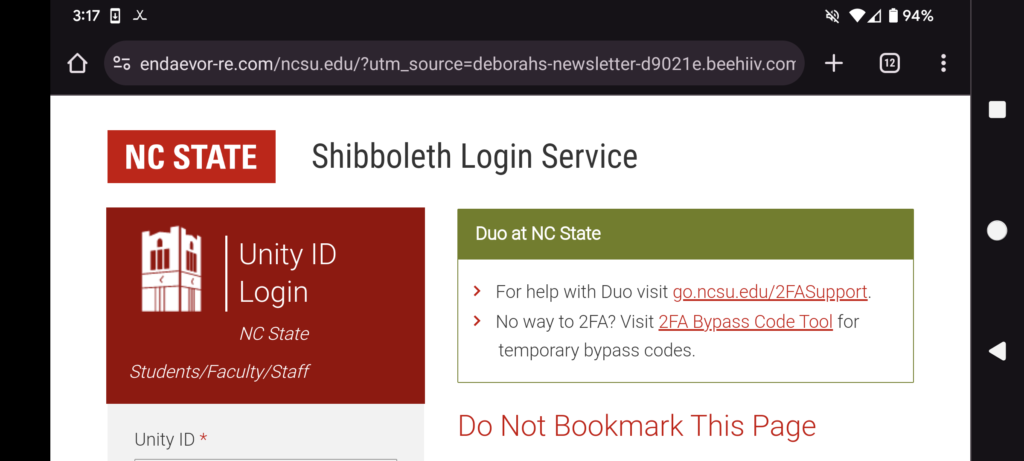
Pictorial Example
Here’s a site that looks identical to the shibboleth log-in page, but the URL is weird. It says things like “endaevor” and “deborah” and “beehiiv” instead of the usual shib.ncsu.edu. This is also on a phone, which tend to be more difficult to read URLs on, and therefore easier to be phished on!
Protect yourself from phishing attacks
- Remember that IT Staff will never ask you for your password
- Have 2-factor authentication enabled on as many accounts as you can
- Never re-use passwords
- Always look closely at the URL, especially on mobile, when entering personal information.
- Always look at the sender of an email. You may also try to ensure that it is Authenticated.
- Always report phishing emails if they make it through your spam filters.
- Avoid sharing personal information, under the pressure of urgency, if you do not know the entity on the other side.
- Never share 2FA codes over the phone. If someone on the phone claims that you need to accept a 2FA push notification, do not do so and change your password immediately.
- Never trust calls that demand the ability to remote into personal machines.
- Report suspected phishing attempts following these instructions.
These lists are not exhaustive, though we’ve tried to keep them full of recent examples. Phishers will change their tactics as time passes; ultimately, you should always exercise caution and guard personal information or machine access.
If you receive an email that does not look legitimate, do not respond or visit the link and do not provide your personal information to unknown sources. Please note that the university will NEVER ask you to send personal information through email.
1 Much of this page was authored by Aleksander Nahapetyan, as his research is in web security and phishing. ↩
References
