Networking
Learning Outcomes
- Identify general features in networking, hardware and operating systems
- Operate engineering software on personal and lab computers
- Send and receive e-mail and use other campus computing services
Chapter Learning Outcomes
- Identify and describe different networking mediums such as twisted pair cables, fiber optics, and wireless communication.
- Identify the basic function of common networking devices (e.g., routers, switches, firewalls) in enabling internet access and local network communication.
- Use SSH to log into remote computers
- Use RDP to access applications remotely
- Networking is fundamentally about transmitting information between two devices1
- Communication is now possible between any two devices anywhere (just about).
NC State provides services and networks to connect its users to the campus computing system using wired and wireless connections. This network provides access to the following areas:
- Web-based Services
- Unix/Linux Applications
- Virtual Computing Lab
- Secure File Transfer
Any of these resources can be accessed from any machine or operating system, regardless of geographical location, via the Internet.
Browsers and Cookies
Browsers
The most likely applications you will use on your computer are the browser, text editors, and terminal. Let’s talk about the browser! Popular browsers include Chrome, Edge, and Firefox.
Shortcuts
Getting familiar with common shortcuts can really pay off in the long run to navigate within your browser. Note that Ctrl probably maps to Cmd on a Mac.
- Middle Button Click in a link opens it in a new tab
- Ctrl+T Opens a new tab
- Ctrl+Shift+T Reopens a recently closed tab
- Ctrl+L selects the contents of the search bar
- Ctrl+F to search within a webpage.
Search operators
Web search engines like Google or DuckDuckGo provide search operators to enable more elaborate web searches:
- “bar foo” enforces an exact match of bar foo
- foo site:bar.com searches for foo within bar.com
- foo -bar excludes the terms containing bar from the search
- foobar filetype:pdf searches for files of that extension
- (foo|bar) searches for matches that have foo OR bar
More advanced search operators are available for popular engines like Google and DuckDuckGo
Searchbar
The search bar is a powerful tool too. Most browsers can infer search engines from websites and will store them. By editing the keyword argument, you can create fast searches on specific websites (for example, you may use YouTube or Wikipedia often and want to search them directly).
- In Google Chrome they are in chrome://settings/searchEngines
- In Firefox they are in about:preferences#search
Cookies Add State to HTTP
Many features on the web require maintaining some form of state. For example, when you log into your email account, you can stay logged in across many requests and responses. If you enable dark mode on a website and make subsequent requests to the website, you want the pages returned to have a dark background. If you’re browsing an online shopping website, you want the items in your cart to be saved across many requests and responses.
However, HTTP is a stateless protocol, which means each request and response is independent from all other requests and responses. Thus, browsers and servers store HTTP cookies so a server to recognize repeat visitors. Think of cookies as pieces of data stored in your browser. These cookies encode state that should persist across multiple requests and responses, such as your dark mode preference or a list of items in your shopping cart. In future requests, your browser will automatically attach the relevant cookies to a request and send it to the web server. The additional information in these cookies helps the web server customize its response.
Each cookie is just a name, value pair. For example, a cookie darkmode=true has name darkmode and value true.
If domain of cookie matches domain in the url, then cookie is a “first party” cookie. Otherwise, it’s a “third party” cookie.
Cookies are commonly used for:
- Advertising
- Analytics
- Social Media
Privacy extensions
An ad blocker not only blocks most ad content but it will also block sketchy and malicious websites if they are included in the common blocklists. They will also reduce page load times sometimes by reducing the amount of requests performed. You may like to investigate the following privacy extensions (installing not required by this class).
- uBlock origin (Chrome, Firefox): block ads and trackers based on predefined rules.
- Privacy Badger: detects and blocks trackers automatically. For example when you go from website to website ad companies track which sites you visit and build a profile of you
You can find about more addons of this kind here.
If you’re interested in seeing just how identifiable you are when you browse, check out Cover Your Tracks.
References
- CS 161 Cookies
- Missing Semester, MIT, 2020
- Content acknowledgement: Brad Reaves
Protocols
In life, protocols define the way we interact with other people. In computer science, protocols are rules that dictate the ways in which computers communicate with one another over a network medium2.
Examples of protocols include:
- HTTP (Hypertext Transfer Protocol): Used for transmitting web pages over the Internet.
- FTP (File Transfer Protocol): Used for transferring files between a client and a server. (FileZilla uses SFTP, secure file transfer protocol)
- TCP (Transmission Control Protocol): Data transport between machines across networks
- IP (Internet Protocol): Handles addressing and routing of packets between devices.
- Ethernet: transmits data over a cable.
Connecting to the Network
- Each computer connecting to the network has a unique Internet Protocol (IP) Address. This address acts like a unique postal code, telling other computers where to send information on the network.
- Internet Protocol version 6 (IPv6) is the current standard protocol used to route traffic across the internet. IPv6 addresses are 128 bits. The earlier protocol, IPv4, uses 32 bits. IPv6 supports 2128 (about 3.4×1038) addresses, vs. the 232 supported by IPv4.
- IPv4 addresses are usually written as 4 integers between 0 and 255, such as
128.32.131.10. IPv6 uses 128-bit IP addresses, written as 8 2-byte hex values separated by colons, such ascafe:f00d:d00d:1401:2414:1248:1281:87123 - IPv6 helps with us running out addresses.
- IPv4 addresses are usually written as 4 integers between 0 and 255, such as
Domain Names
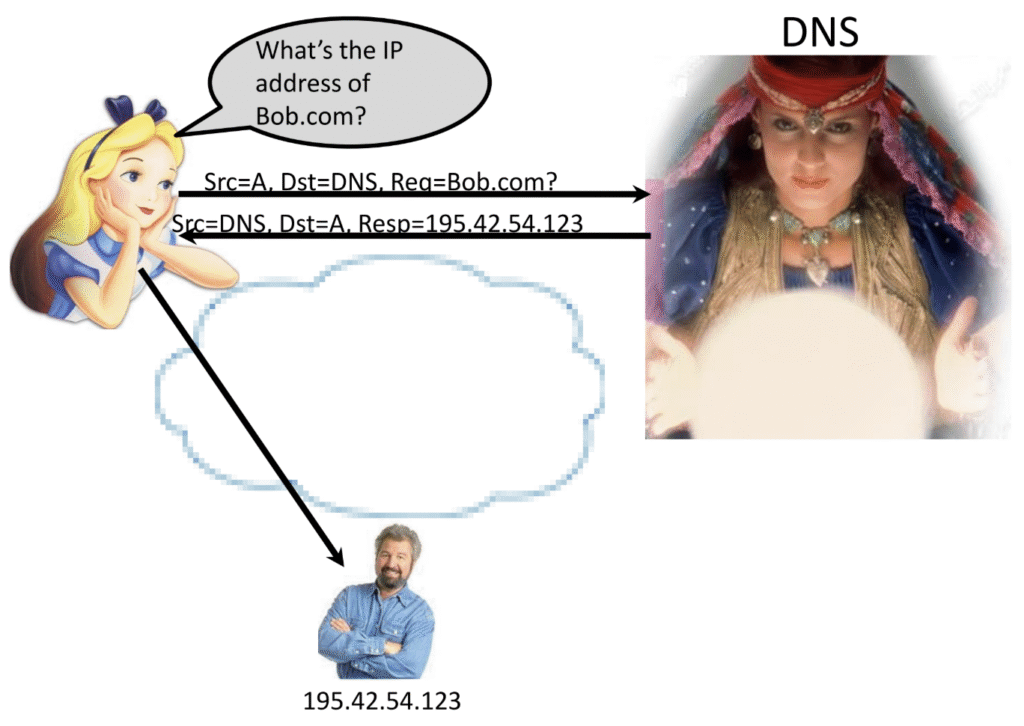
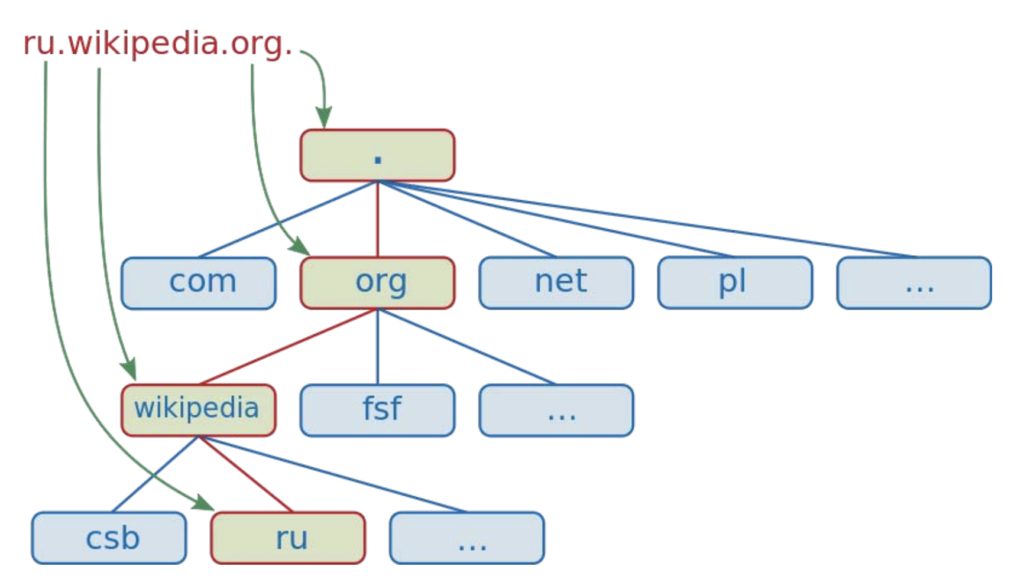
DNS (Domain Name System) translates domain names that you type in the URL bar (e.g., “www.google.com”) into their corresponding IP addresses, allowing your web browser to find the correct server.
Domain Names Are Hierarchical
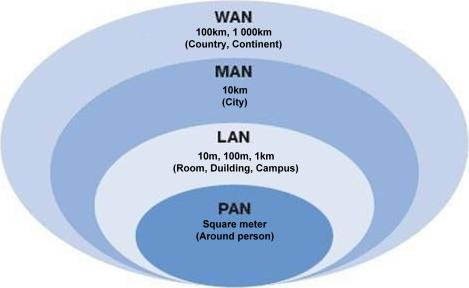
Area Networks
| Type | Scope | Ownership | Examples |
|---|---|---|---|
| LAN | Local (building) | Private (e.g. home, school) | Connected via switches |
| WAN | Large, often global | ISPs and corporations | Internet access, leased lines |
| MAN | City-wide | ISPs or private networks | Office-to-office city links |
| VLAN | Virtual, logical grouping | Software-defined | NC State network setup |
Exercises4
- What is the difference between the Internet and the World Wide Web? Create at least three statements that identify the differences between the two.
- Who are the broadband providers in your area? What are the prices and speeds offered?
- Pretend you are planning a trip to three foreign countries in the next month. Consult your wireless carrier to determine if your mobile phone would work properly in those countries. What would the costs be? What alternatives do you have if it would not work?
- Check the speed of your Internet connection by going to the following web site: speedtest.net
What is your download and upload speed? - What is the IP address of your computer? How did you find it?
- The ping command allows you check connectivity between the local host (your computer) and another host. If you are unable to connect to another host, the ping command can be used to incrementally test your connectivity. The IP address 127.0.0.1 is known as your home address (local host).Begin your test by going to your command line interface and pinging your local host: ping 127.0.0.1. You should get a series of “Reply from 127.0.0.1” messages. Use Ctrl+C to stop the responses.
- Sometimes a failed ping is not the result of a lack of connectivity. Network administrators of some IP addresses/hosts do not want their site pinged so they block all ICMP packets. That’s the protocol used for pinging.
- On a UNIX-based system, you may have local table of IP addresses to websites called
/etc/hosts. If you want to read it, trycat /etc/hostsfrom the command line.
Footnotes/References
- Content from CSC 474. Acknowledgments to William Enck, Brad Reaves, Micah Sherr, Patrick McDaniel ↩︎
- Reference: CS402 Saylor ↩︎
- Reference: CS161, UC Berkeley, Ch 25. ↩︎
- Information Systems for Business and Beyond (2019) by David Bourgeois ↩︎
